Third-Party Risk Management (TPRM)
Third party risk management is a procedure for assessing, identifying, and reducing risks associated with outsourcing businesses, which includes third party vendors, suppliers, or business partners related to security breaches, financial losses, and legal violations. TPRM helps organizations to minimize their business risks from cyber-threats, allowing them to stay updated with security compliance. TPRM provides different security solutions to organizations that help them to analyze vulnerabilities in safety controls and to fix them before any consequences arise.
Third party risk management also protects organizations from any reputational damage due to security breaches or any regulatory non-compliance. TPRM ensures that all third parties involved with associated businesses and all their potential risks are thoroughly covered against, security breaches, operational failures, non-compliance, and reputational damages.
Third-Party Risk Categories:
Operational Risk: This refers to system or process failure while performing any operational task. TPRM handles such risks for a smooth procedure and avoids business interruptions.
Financial Risk: When companies bear financial losses due to negligence in proper analysis and early stage threat detection can go through financial risks in their business. Any external factor can diminish companies’ sales growth.
Compliance Risk: Companies can fail to comply with legal regulations, as they need to adhere all regulatory authorities’ guidelines. Meeting every guideline on time is an important task that can sometimes be skipped, resulting in legal violations and penalties.
Reputational Risk: Businesses that are performing well in the market and have gained strong trust, as a top service provider need to maintain their name and fame. Failing in any of the services can lead to public disgrace and reputational damage to the business.
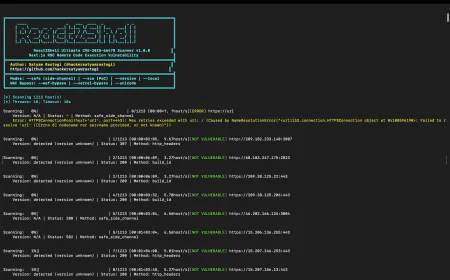
Cyber Risk: Businesses can also face cyber-threats while operating in internet zones. These cyber threats can harm organizations in various ways such as data breaches, illegal system hacking, or any other security issues.
TPRM (Third Party Risk Management) Life Cycle:
Planning: This is very first step for businesses while they plan to engage any third party partner to expand their current services to customers. Organizations should evaluate their business needs thoroughly and determine if any external business partner is necessary. Once the analysis is complete, they should plan everything properly including the vendor’s previous services, their relationships with associated partners and most importantly the security posture they provide, before hiring any vendor.
Cross Verification: Business partners are required to validate each other before starting any new assistance. Companies are required to verify their supportive partners to ensure they can matchup with the currently provided services and vice versa to the vendors if they can smoothly merge their extra services with joined organizations.
Negotiation & Onboarding: Once an organization has selected its vendor to work with it starts working on contractual negotiations. They need to discuss on business risk strategies, work ethics, and service expectations. Both parties should establish a clear and strict responsibility guidelines and Service Level Agreements (SLAs). Once both parties accept all terms and conditions, they move on to the next level of onboarding third party services.
Constant Monitoring: When companies tie-up with external vendors they are required to monitor their performance regularly. They should conduct regular audits and daily assessment of third party’s performance to check if they are adhering all contractual conditions or making any changes. Regular monitoring and performance reviews throughout the lifecycle ensure “no service disruption”.
Risk Management: Mitigating the risk through external operational channels in the business is one of the most important steps of TPRM lifecycle. Effective risk management can minimize the addition of any third parties’ services to current business, which can increase operational supply chain risks and service disruptions. The TPRM program detects issues quickly and sends automatic notifications to stakeholders to respond immediately.
Offboarding: Organizations should implement service expiration terms and termination of third party services in case of breaches. Such terms push vendors to stay alert regarding their security controls and adhere to the legal guidelines efficiently.
Renewal of Contracts: Appropriate business behavior and quality of the third party services lead to an extension with their provided services as their associated partners wish to renew the contract period and its extended services.
Third Party Risk Management (TPRM) Obstacles and Solutions:
Lack of Clarity: Many vendors at a time for various tasks can create confusion in handling them appropriately. This confusion can raise serious concerns for companies to run their business properly.
Solution: Properly bifurcated document records of all onboarded vendors help companies handle them in a mannered way without any puzzlement.
Incomplete Data Sharing: Many vendors or third party business partners hesitate to share their complete internal data with associated organizations. Most do not provide crucial documents as they are scared of their internal information breaches as well. This insecurity poses challenge for the third party risk management system.
Solution: Enforcing a strict and mandatory vendor questionnaire and clearly defined security solutions for third party vendors or partners ensures they share detailed information with their associated businesses. Providing strong safety guidelines boosts their confidence not to hide any necessary internal data while processing business onboard.
Poor Vendor Selection: Sometimes to meet the business deadlines companies do not verify their vendors properly and hire them without checking their background and security measures.
Solution: Companies should not rush the vendor onboarding process at all. They should streamline their deadlines accordingly and take adequate time to verify their external business partners to prevent future incidents.
Manual Data Handling: Most of the businesses still use manual spreadsheets for vendor details maintenance. Manual data handling creates human errors and slows down the business process.
Solution: Opting for advanced data handling software will completely resolve this problem of manual data maintenance. System oriented records are error free and more reliable than human efforts.
Inefficient Monitoring: Companies do not pay sincere attention to constant vendor monitoring. Usually they monitor in initial stages only then it becomes irregular and inefficient, which creates business chaos later on.
Solution: Using automated third party risk management software helps businesses to keep real time records of all vendors and provides them accurate system analysis. This technology ensures continuous and efficient system monitoring preventing any unauthorized access.
Compliance Pressure: Regulatory authorities pressure organizations for security compliance on time. Companies are forced to perform in hustle way due to such regulations.
Solution: Organizations can simply opt for automated compliance software to keep them compliant at all times. An advanced auto compliance system eases the workload of gathering legal documents every time and assembling them for audits is a complete mess and an extra effort for the staff.
Highly Cost Impact: Maintaining detailed information of every vendors is very cost effective for small and medium sized businesses. For their cost savings, such companies do not opt for third party risk management and run their business with risks.
Solution: Understanding the business criticality and prioritizing its safety measures persuade companies to enforce necessary guidelines without much affecting their financial costs. They can easily opt for suitable safety solutions to their businesses.
Complex Onboarding: Onboarding of any third party vendor in business is very complicated and time consuming. This complication also holds companies back from opting for TPRM.
Solution: AI-driven portals can simplify this lengthy process with system-based questionnaires and speed up the onboarding process.
Uncategorized Risks: When organizations do not divide their business criticality into various categories, can harm their smoothly running operations. They can divide these risks into Low, Medium, and High.
Solution: Businesses need to categorize their business criticality into different levels such as High, Medium, and Low. Categorizing risks will provide a clear picture to prioritize business threats and proceed accordingly.
Why Third Party Risk Management (TPRM) Matters?
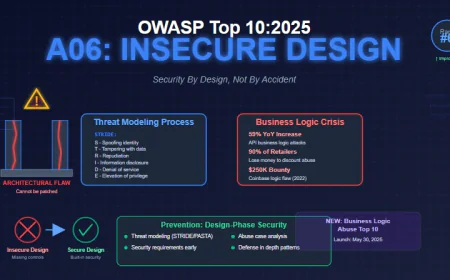
TPRM is crucial for modern growing businesses as they expand their business with outsourcing partners or contractors. They need to run their business smoothly with all the safety measures belong to any third party integration. When outside vendors come into the role organizations should be extra alert for their security controls to avoid safety breaches.
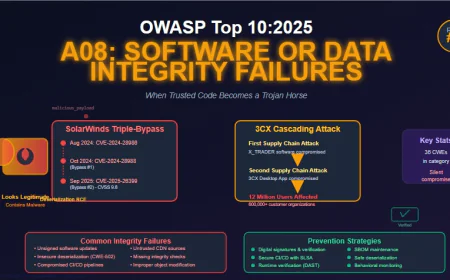
Supply-Chain Risk Prevention: Attackers can easily exploit vulnerabilities through vendors’ weak security postures. TPRM prevents such incidents applying strong data protection solutions.
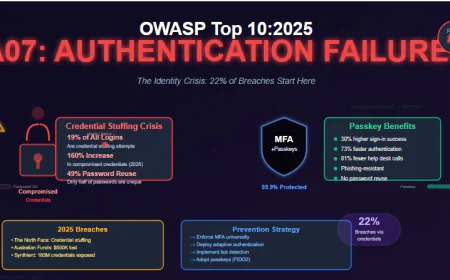
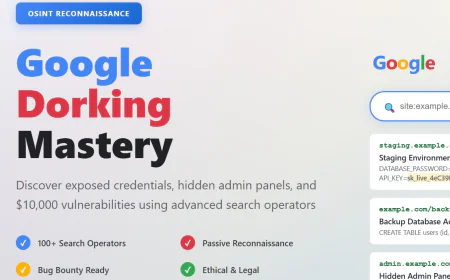
Cyber-Threat Protection: Cyber-crimes always search for secret backdoors to attack, which is easier through third party insufficient security controls. With the help of TPRM this loophole can be fixed and protecting sensitive internal information from breaches.
Compliance Management: TPRM helps businesses to comply with legal authorities without failure. It supports companies to stay updated and adhere all safety guidelines efficiently to avoid violations and penalties.
Smooth Operations: Once vendor onboarding is completed properly and third party risk is fully protected, supplier’s failure also cannot halt the business operation. Therefore, the reason TPRM plays a vital role in business outsourcing process.
Brand Reputation: Third Party Risk Management also protects business reputation from public criticism because of third party failure or any unethical practices.
Minimize Financial Loss: Effective risk management prevents financial losses due to operational or security failures. Such incidents are fully protected under TPRM.
External Access Control: When businesses expand with external partners they can have secure third party access control to avoid sensitive data leakage only with the TPRM.
Vendor Risk Management: Effective risk management allows companies to verify their external business partners thoroughly and investigate their backgrounds in previous partnerships. An appropriate evaluation mitigates the risk of vendor failure.
Conclusion
While deeply analyzing every aspect of business criticality the term Third Party Risk Management absolutely fits to any organization. When companies grow positively with trusted services they definitely uncover new ideas to expand their services to customers and this spread needs a control over new and unexpected operational troubles. Effective risk management in any organization ensures operational safety and provides confidence to run their business flawlessly.