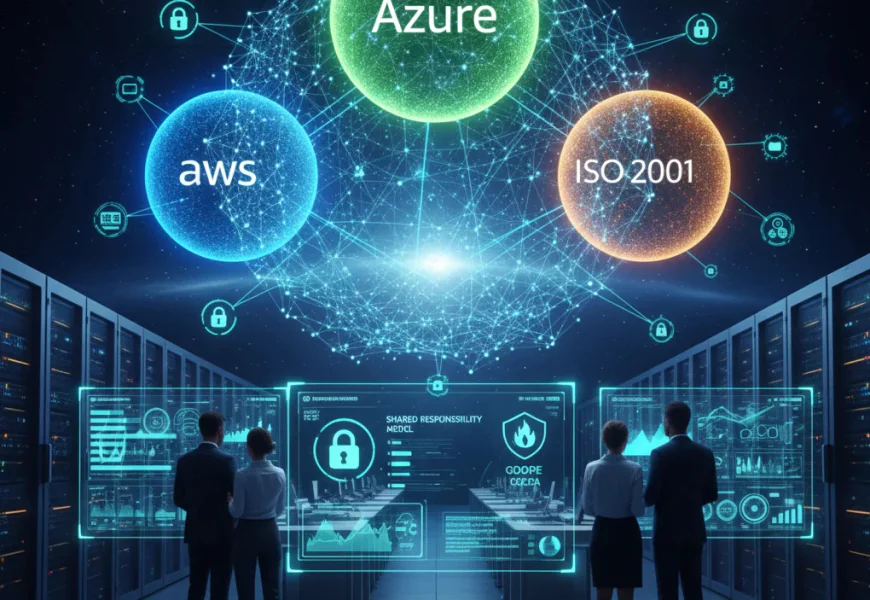
Multi-Cloud Security & Compliance
Multi-cloud security is a complete security solution that protects companies, customer data, assets and applications from advanced security threats. Multi-cloud security is a service that protects organization’s data across multiple cloud providers. By using multiple clouds we can protect our sensitive data more precisely than usual.
Introduction:
Multi Cloud Security provides a combined security service that allows organizations to save their customers’ sensitive data efficiently using various cloud services. Multi service providers offer different security solutions that can protect systems from advanced risks with their threat detection policies.
By distributing system workloads to multiple clouds improve performance. If any of the service provider becomes unavailable or is stuck with functionality, other clouds can resume that system task immediately without any hurdles.
Advantages of Multi-Cloud-Security:
Combined Visibility and Control: Centralized security tools provide clear visibility and a strong control over multiple cloud services. They can detect advanced threats and serve a quick response.
Improved Security Point and Compliance: Centralized security management improves the quality of safety measurements. It helps to understand and analyze security position better and streamlines regulatory adherence.
Increased Adaptability: Multiple security services offer more flexibility to choose better and advanced services for work ethics. New updates and improved security features make systems more efficient and ready to adapt new challenges.
Increased Loss Recovery: Using various cloud services increase safety measures. These different solutions enhance security parameters for faster loss recovery. Multiple features can detect risks at an early stage which helps avoid any financial losses.
Enhanced performance: Multi-cloud management provides different resources for better performance allowing workloads to be distributed among all rather depending on one.
Access to Best Service Provider: Using multi cloud enables the selection of the best service provider among all. We can apparently compare the features between cloud providers and easily find the one that is suitable for business growth.
Advanced Threat Detection: Various clouds can perform distinctively with their advanced features. This helps organizations stay alert for any potential threats detected by the security system.
Reduced Single Vendor Reliability / Eliminate Vendor Lock-In: Working with more than one service vendor simply protects from single vendor lock-in. Which means if any of the cloud providers become unavailable another cloud can pick-up that workload and perform smoothly.
Challenges:
Though multi cloud security has its numerous benefits but responsibilities always come with challenges. Organizations can enjoy different benefits from using various security services, also they have to handle some difficulties too. Here are some challenges that need to be handled appropriately.
Complexity: While using multiple cloud providers, companies can face complications with different management tools. Each service provider has a different architecture for functioning, this diversity can create difficulties in understanding initially.
Broad Visibility: Using more than one cloud service requires wide or comprehensive visibility. A clear and broad vision among all cloud solutions helps organizations to perform better. However, this responsibility becomes a significant challenge for them in early stages.
Extended Threat Surface: Although, working with multiple services offers many opportunities but this divided workload can seems as a large surface area that attracts cyber threats. Once attacker can get through one platform this increases the risk of unauthorized access among other clouds also. This can be avoided by adhering to strong security protocols across all cloud services used within the organization.
Constant Monitoring: Implementing multiple security solutions seeks constant monitoring of the system. This multi-tasking effort can be monotonous or disheartening sometimes. One small lapse in attention can turn into a serious hazard for the organization.
Combination Architecture: When acquiring different security services from multiple providers, companies need to manage various security solutions simultaneously. Every cloud service provider has its unique architecture for functioning this service combination can be a time consuming task for human experts to handle.
Advanced technology and better services always come with some exceptions but keeping everything streamlined and working on vulnerable areas can minimize the probabilities.
Multi-Cloud Compliance
Multi-Cloud compliance refers to managing all cloud service providers with appropriate actions and adhering all legal guidelines among those providers for customer’s data security.
Cloud compliance is a framework for managing data breach risks while storing and processing in a cloud network. Companies must build an ethical work environment that complies with laws and regulations.
Organizations need to follow every instruction enforced by security law standards. They should comply with compliance rules without failure for better and improved performance to run a successful business. Ignoring any of the regulations and failing to comply efficiently can create a big trouble such as financial penalties or discontinuation of services.
Prioritizing customer’s data security should be the focus of any security service provider. Being well compliant with regulations builds strong safety trust among all (service provider-organization-customer) and gives a confidence for secure operations.
Acquiring multiple services improves business performance efficiently but these services need to be compliant at all times. They should not avoid any given guidelines and companies are more responsible for their better functioning.
Cloud-Compliance Standards
The government has set some standards for companies to comply with their data security. They should follow the guidelines of each compliance framework to avoid legal violations. Security compliance is mandatory for all organizations that store, process, and manage customers’ personal information. It can be any identifiable and sensitive data that has been shared by customers for their digital operations. There are some mandated regulatory compliance standards that audit and control organization’s work ethics and their security culture.
GDPR (General Data Protection Regulation): GDPR protects European residents’ personal data that has been saved for digital operations by reputable organizations and ensures their security from data breaches.
HIPAA (Health Insurance Portability and Accountability Act): This regulation controls medical institutes. These health companies generate, save, and process patients’ personal medical details that needs to be fully protected. HIPAA enforces strict guidelines on these health companies to ensure patients’ sensitive and personal medical information is completely secure with them and that no health data is processed without patient consent.
PCI DSS (Payment Card Industry Data Security Standard): PCI DSS focuses on data security and controls for those organizations that store and manage credit card details. These companies are responsible for saving and processing customer’s credit card details, such as card numbers, safety pins or other personal information used for digital payments or transactions. Trusted companies needs to ensure their data safety by efficiently adhering the rules and complying with these regulations.
FedRAMP (Federal Risk and Authorization Management Program): FedRAMP is a U.S. government program that authorizes all cloud products and services. It provides security assessments and continuous monitoring of cloud services whether they are working efficiently or not. It is designed to protect the government’s sensitive information. Companies that provide cloud services to the government must comply with their regulations only then are they authorized to serve in the government-wide program.
ISO/IEC 27001: It is an international standard for implementing and maintaining ISMS (Information Security Management System) for cloud services.
SOC2 (Service and Organization Controls 2): This framework evaluates service providers systems are fully secure for use and manages their operational controls. It ensures that customer data is completely protected from any unauthorized access in cloud environment.
NIST SP 800-53: NIST Special Publication 800-53 is a security standard that provides a catalog of privacy and security controls for federal information systems.
CCPA/CPRA (California Consumer Privacy Act/California Privacy Rights Act): This privacy act is enforced by the U.S. government for their customers who live in California. It is specially designed to protect California residents’ personal data that is collected by responsible organizations. CCPA ensures their residents that any personal and sensitive data shared by them with a reputable organization, is completely secure from data breaches. Responsible organizations need to comply efficiently with this regulatory authority to avoid any legal violations related to people data safety.