Vercel Security Incident Highlights Growing Risks of AI Integrations and OAuth Exploitation
The recent Vercel security incident reveals how attackers are exploiting third-party AI tools and OAuth integrations to bypass traditional defenses. This blog breaks down how the breach happened, why it matters, and how organizations can protect themselves against similar supply chain threats using proactive cybersecurity strategies.
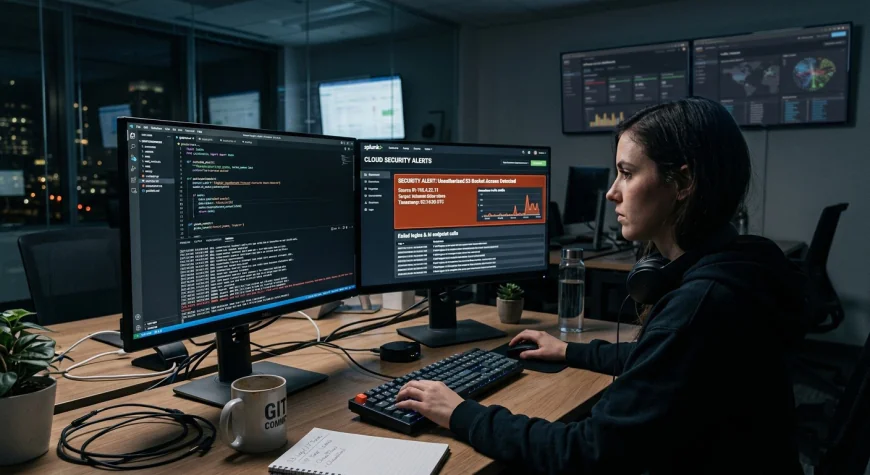
A security event at Vercel has again brought to light a significant change in the methods employed by cyberattackers today. Rather than attacking any particular infrastructure, the attacker is now leveraging third-party integrations that are linked via AI platforms and OAuth authentication.
The breach was not initiated because of any flaw in Vercel’s own software architecture. On the contrary, the attack was launched via a third-party AI application called Context.ai. From there, the hacker was able to access a Vercel employee’s account.
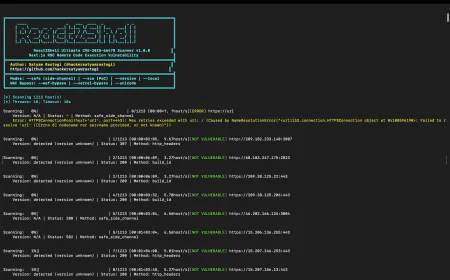
How the Attack Unfolded
The attack chain also shows the rise of the current cybersecurity strategy where hackers use trust relationships to perform attacks instead of forcing themselves into the systems.
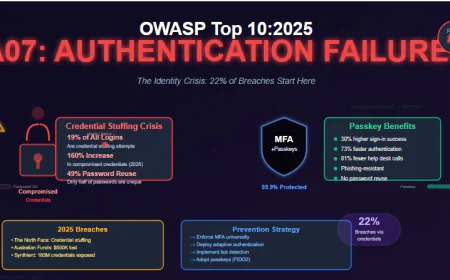
The hacker had used OAuth permissions and tied the Context.ai to their Google workspace. Then, the attack was conducted on the compromised AI tool to get access to the resources without using passwords or getting through the multi-factor authentication process.
This technique is quite efficient as the OAuth access tokens provide persistent access within a trustworthy environment. In this case, hackers disguise themselves among the other legitimate users, making it harder to detect the threat.
Following this, the hacker was able to access several internal resources of the Vercel system. The access allowed him to see some environment variables and data on the system level. At the same time, Vercel assures that all the sensitive encrypted data was secured.
Why This Incident Matters
At first glance, the impact may appear limited. However, the implications are much broader.
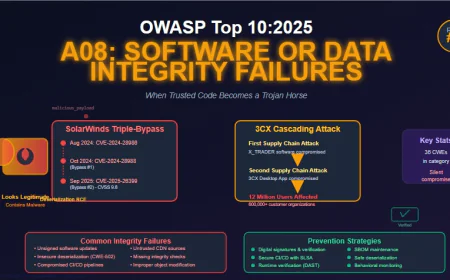
This incident highlights three major issues shaping today’s threat landscape:
1. Third-Party Integrations Are a Primary Attack Vector
The organization depends on the external systems because it requires these systems to increase its efficiency in operations. This connection leads to extra ways in which the systems can be breached. This was made possible by an external platform that had access to the systems of Vercel.
2. OAuth-Based Access Is Increasingly Targeted
OAuth is meant to make authentication easier, but it establishes lasting trust relationships as well. Attackers who manage to steal a token can work inside a system without raising any alarms. As such, exploiting OAuth has become one of the most rapidly increasing attack methods.
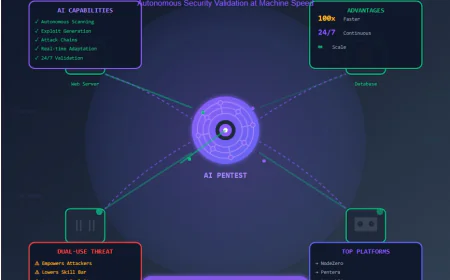
3. AI Tools Are Expanding the Attack Surface
The incorporation of AI-based technologies is progressing rapidly within development and business activities. Nevertheless, security measures concerning such technologies are currently undergoing development. A significant number of companies grant unrestricted access without comprehending the associated threats.
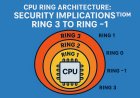
The Real Risk: Identity Over Infrastructure
This attack on Vercel demonstrates the major shift happening in the domain of cybersecurity. These attackers will now be targeting the identity and not seeking any vulnerabilities in the infrastructure.
By attacking a single point of integration, the attackers can circumvent all the security protocols set up to enter the network internally.
The twist in the tale is that most companies will have no idea that an attack has occurred before they become victims themselves.
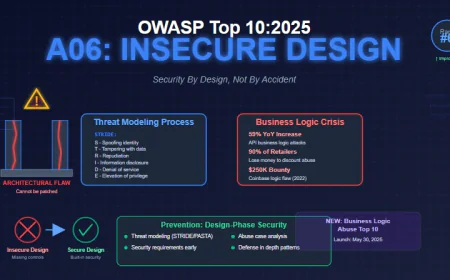
Where Organizations Fall Short
Most security strategies are still built around protecting internal systems—firewalls, endpoint protection, and network monitoring. While these remain important, they are not sufficient against modern threats.
The key gaps include:
-
Lack of visibility into third-party integrations
-
Limited monitoring of OAuth permissions and activity
-
Inability to detect exposed credentials outside internal environments
-
Over-reliance on trust without continuous validation
These gaps create opportunities for attackers to exploit indirect access points, as seen in the Vercel case.
How IntelligenceX Helps Bridge the Gap
This is where IntelligenceX plays a crucial role in strengthening cybersecurity posture.
IntelligenceX gives businesses visibility into exposed data, compromised passwords, and attacker infrastructure on the internet. In cases where the incident occurs outside of the control of the business, such as in the case of Vercel, IntelligenceX visibility is crucial to understanding the attack.
With IntelligenceX, organizations can:
-
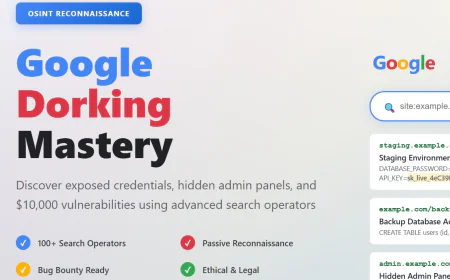
Get all your exposed API keys and credentials identified before attackers find them
-
Monitoring domains known to be infested: This phrase may be simplified
-
Please identify any data leaks or access tokens being circulated in external sources?
-
A tool that can experience the launching of trigger operations as per one's necessities when a certain action happens is known as 'Webhook'.
By extending security beyond internal boundaries, IntelligenceX helps organizations identify risks early and respond proactively.
Lessons from the Vercel Incident
There are several key takeaways that organizations should consider:
- Audit Third-Party Access Regularly
Every integration should be reviewed periodically. Unused or unnecessary permissions should be revoked immediately. - Limit OAuth Permissions
Grant only the minimum level of access required. Avoid broad or unrestricted permissions whenever possible. - Monitor for Suspicious Activity
Logs and activity data should be continuously analyzed to detect unusual behavior. - Treat External Tools as Potential Risks
Even trusted platforms can be compromised. Security policies should always reflect this reality. - Invest in External Threat Intelligence
Internal monitoring alone is not enough. Organizations need visibility into threats originating outside their environment.
Final Thoughts
Organizations acquire AI systems together with their third-party components, which results in a continuous growth of their vulnerable areas. The traditional security systems which protect physical infrastructure need to be replaced with better security systems. Digital ecosystems demand modern security solutions which provide complete visibility for monitoring and intelligence operations. Security requirements now need better protection systems which detect all kinds of modern digital threats.
IntelligenceX has emerged as a vital platform which organizations need to operate their businesses successfully. IntelligenceX provides organizations with operational intelligence about their external threats because of their exposed data, which helps them defend against attackers while decreasing their risk exposure.
Security now needs to operate before problems develop because people can misuse trust while they turn access into a security weapon. Security has become a requirement that must be met.