DDoS Attack : How to Protect your Business
A distributed denial-of-service (DDoS) attack is a malicious attempt to disrupt the normal traffic of a targeted server, service or network by overwhelming the target or its surrounding infrastructure with a flood of Internet traffic.

DDoS attacks achieve effectiveness by utilizing multiple compromised computer systems often distributed globally as sources of attack traffic. Exploited machines can include computers and other networked resources such as IoT Devices
From a high level, a DDoS attack is like an unexpected traffic jam clogging up the highway, preventing regular traffic from arriving at its destination.
How does a DDoS Attack Work?
DDoS attacks are carried out with networks of Internet-connected machines.
These networks consist of computers and other devices (such as IoT devices) which have been infected with malware, allowing them to be controlled remotely by an attacker. These individual devices are referred to as bots (or zombies), and a group of bots is called a botnet.
Once a botnet has been established, the attacker is able to direct an attack by sending remote instructions to each bot.
When a victim’s server or network is targeted by the botnet, each bot sends requests to the target’s IP address, potentially causing the server or network to become overwhelmed, resulting in a denial-of-service to normal traffic.
Because each bot is a legitimate Internet device, separating the attack traffic from normal traffic can be difficult.
How to Identify a DDoS Attack?
The most obvious symptom of a DDoS attack is a site or service suddenly becoming slow or unavailable. But since a number of causes — such a legitimate spike in traffic — can create similar performance issues, further investigation is usually required. Traffic analytics tools can help you spot some of these telltale signs of a DDoS attack:
- Suspicious amounts of traffic originating from a single IP address or IP range
- A flood of traffic from users who share a single behavioral profile, such as device type, geolocation, or web browser version
- An unexplained surge in requests to a single page or endpoint
- Odd traffic patterns such as spikes at odd hours of the day or patterns that appear to be unnatural (e.g. a spike every 10 minutes)
- Unexplained server error messages, timeouts, or the inability to access your website
- Notification from Internet service provider (ISP), cloud service provider (CSP), or other service provider
Some Common Types of DDoS Attacks
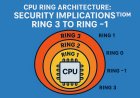
Different types of DDoS attacks target varying components of a network connection. In order to understand how different DDoS attacks work, it is necessary to know how a network connection is made.
A network connection on the Internet is composed of many different components or “layers”.
The OSI (Open System Interconnection) model, is a conceptual framework used to describe network connectivity in 7 distinct layers.
While nearly all DDoS attacks involve overwhelming a target device or network with traffic, attacks can be divided into three categories.
· Volumetric (Gbps)
· Protocol (pps)
· Application layer (rps) attacks.
Since these three are categorized as DDoS attacks, the terms are often confused or used interchangeably by accident. Complicating matters, there are times when these types of DDoS attacks overlap during a single attack to generate greater impact.
Attackers don’t make clean distinctions between these three types of DDoS attacks. Their goal is to disrupt your business. When attacking their target, they’ll combine volumetric, protocol, and application layer attacks into a multi-vector attack. Multi-vector attacks hit the target in varying forms and disrupt the processes at a higher level.
Gbps or Volumetric DDoS Attack
A volumetric DDoS attack is what most people associate with the term “DDoS” because it is the most common. The first volumetric DDoS attack made headlines in the late 1990s and has since spawned an army of copycats.
Volumetric attacks can also be called “floods” because an attack floods a target’s server with requests, like unwanted pings. Attacks are measured in bits per second (bps) or Gigabits per second (Gbps).
The concept of a volumetric attack is simple: send as much traffic as possible to a site to overwhelm the server’s bandwidth. Volumetric attacks are typically produced using amplification techniques. DNS amplification is one of the more common techniques attackers use to carry out a volumetric attack. The bad actor sends small DNS requests with the victim’s spoofed source IP address to a DNS server. When the server receives the request, it responds to the victim with a large response.
Attackers also create volumetric attacks using botnets made up of exploited IoT devices. Connected devices usually lack basic security defenses, but because they’re connected to the Internet and can execute code, they can be easily exploited.
The proliferation of cheap IoT devices like toys, small appliances, thermostats, security cameras, and Wi-Fi routers makes it easy to launch an effective attack with just a few clicks. A hacker can easily leverage the extensibility of the internet to launch a successful volumetric DDoS attack with few resources.
The Mirai botnet is an example of the devastation of leveraged, unsecured IoT devices. Mirai targeted IoT devices, using each infected device to join a volumetric DDoS attack. It resulted in successful attacks against some of the world’s largest organizations.
PPS or Network Protocol DDoS Attack
An internet protocol is a discrete set of rules for exchanging information across the internet. TCP/IP is one of the most well-known rules for exchanging requests and data. A bad actor can severely disrupt an online service by exploiting these rules.
Protocol attacks often work at layers 3 and 4 of the OSI model on network devices like routers. Because they are on the network layer, they are measured in packets per second (pps).
Below is a sampling of different network-layer DDoS attack types:
· UDP floods
· SYN floods
· NTP amplification
· DNS amplification
· SSDP amplification
· IP fragmentation
· SYN-ACK floods
Examples of a Network Protocol DDoS Attack
· The ping of death (POD) is an IP fragmentation attack that exploits the inherent size limitation of a packet. By manipulating parts of the packet or fragments, the exploit can overflow the memory buffers allocated to that packet and then deny service to legitimate packets.
· A TCP SYN flood is another common protocol attack. Here, a surge of TCP SYN requests directed towards a target overwhelms the target and makes it unresponsive.
RPS or Application Layer DDoS Attack
While volumetric attacks and — to a lesser extent — protocol attacks compromise a service with the sheer number of requests, application layer attacks, or layer 7 attacks, target an edge server that executes a web application.
These threats are harder to detect because attackers usually make requests like legitimate users. Consequently, these attacks often show up as smaller traffic spikes and do not require the assistance of a botnet.
Application layer attacks are measured in requests per second (RPS) — the number of requests an application makes. An application layer attack is considered a resource-based attack; therefore, it takes fewer requests to bring down an application because the attack is focused on overwhelming the CPU and memory.
An application layer attack typically includes hitting the web server, running PHP scripts, and contacting the database to load web pages. A single HTTP request, which is simple to execute on the client side, can cause a server to execute many internal requests and load numerous files to fulfill the request, which slows the system.
An application layer attack can also be a multi-vector attack that uses a combination of volumetric and protocol attacks to increase the likelihood of taking a service offline. Because of their complexity and effectiveness, multi-vector attacks are increasingly popular among cybercriminal groups.
The Motivation Behind DDoS Attacks
DDoS attacks are quickly becoming the most prevalent type of cyber threat, growing rapidly in the past year in both number and volume, according to recent market research. The trend is towards shorter attack duration but bigger packet-per-second attack volume.
Attackers are primarily motivated by:
Ideology – So-called “hacktivists” use DDoS attacks to target websites they disagree with ideologically.
Business feuds – Businesses can use DDoS attacks to strategically take down competitor websites, e.g., to keep them from participating in a significant event.
Boredom – Cyber vandals, a.k.a. “script-kiddies,” use prewritten scripts to launch DDoS attacks. The perpetrators of these attacks are typically bored, would-be hackers looking for an adrenaline rush.
Extortion – Perpetrators use DDoS attacks, or the threat of DDoS attacks, to extort money from their targets.
Cyber warfare – Government-authorized DDoS attacks can be used to both cripple opposition websites and an enemy country’s infrastructure.
How DDoS Attacks Impact Businesses?
DDoS attacks pose a significant threat to businesses, causing both immediate and long-term damage. A typical DDoS attack can cost businesses approximately $6,000 per minute, with an average duration of 45 minutes, leading to a total financial impact of around $270,000 per incident. The disruption can have severe consequences, including:
1. Loss of website availability
E-commerce platforms, financial services, and other online services depend heavily on uninterrupted access. A DDoS attack can completely block customer access, leading to missed sales opportunities and operational downtime.
2. Reduced customer trust and reputation damage
Frequent or prolonged service outages caused by a DDoS threat can harm an organization’s credibility. Customers may perceive the business as unreliable or incapable of securing its digital infrastructure, prompting them to seek competitors.
3. Operational disruption
Employee productivity can suffer if internal systems are affected. Additionally, IT teams must divert resources to mitigate the attack, delaying other critical projects.
4. Financial loss
Lost revenue from downtime, recovery costs, and potential fines for service level agreement (SLA) breaches can add up quickly. Large-scale attacks may cost businesses millions of dollars.
5. Security vulnerabilities
In some cases, DDoS attacks are used as smokescreens for other malicious activities, such as data breaches or malware deployment.
To mitigate these risks, businesses need robust DDoS prevention strategies that include real-time monitoring, threat detection, and automated response capabilities to maintain service continuity and protect their reputation.
Steps to Follow after a DDoS Attack
Dealing with the aftermath of a DDoS attack is an important step in enhancing your organization’s resilience. After the attack is over, it's essential to evaluate its impact, reassess your defence strategy, and improve your overall preparedness for potential future incidents. Here are a few recommended key steps to complete this process.
- Analyze the attack post incident by identifying:
- What assets and what part of the network were targeted?
- What DDoS attack method was used?
- How long did the attack last?
- Keep monitoring other network assets for other unusual or suspicious activity, as this might signal the possibility of a subsequent attack.
- Assess the magnitude of the damage to understand its impact on your organization and identify the resources needed for future preventative actions. Key questions to consider include:
- Which services were affected, to what degree, and for how long?
- What were the financial losses incurred?
- Did the attack harm your organization's reputation or lead to customer complaints?
- Were there noticeable impacts on users due to the attack?
- Verify whether your third-party DDoS mitigation service provider has fulfilled their service level agreement (SLA) obligations as expected if you are currently using their services.
- Maintain transparency and effective communication by informing all stakeholders, including employees and customers, about the attack, its impact, and the mitigation steps being taken. Provide consistent updates on the recovery status and anticipated timelines to ensure everyone remains adequately informed. Continue to communicate about additional security measures being implemented to strengthen defences and prevent future attacks as this will demonstrate your organization's dedication to protecting the interests of your stakeholders.
- Identify ways to upgrade your DDoS defence solution. This entails assessing and reinforcing your DDoS protection strategy plan by identifying the root causes and vulnerabilities exposed during the attack. You should explore solutions to bolster your defences at both network and application levels. If you need an extra layer of protection due to limited in-house resources, consider exploring cloud-based DDoS mitigation options or using DDoS protection services from a third-party vendor. Additionally, it's crucial to routinely conduct vulnerability assessment and penetration testing to ensure the effectiveness of your defence solution.
Why is DDoS Mitigation Important?
Distributed Denial of Service (DDoS) attacks are a major threat to all organizations, big or small. Protecting against them is crucial for keeping websites online and preventing business disruptions.DDoS mitigation safeguards revenue, preserves their brand reputation, and prevents costly downtime. By effectively mitigating DDoS attacks, sensitive user data is protected from attackers. Strong mitigation strategies build customer trust by demonstrating a commitment to cybersecurity and data protection, even when facing sophisticated attacks.
What Solutions Defend against DDoS Attacks Best?
Effective DDoS prevention requires a comprehensive approach, blending advanced technologies and strategic practices to mitigate threats. Below are key solutions for DDoS attack prevention and maintaining business continuity:
1. Web application firewalls (WAFs)
WAFs help block malicious traffic targeting web applications. This can be effective for stopping layer 7 DDoS attacks. This will protect the server from malicious traffic, serving as a critical defense against application-layer DDoS attacks.
2. Black hole routing
This technique redirects malicious traffic to a null route or “black hole,” effectively dropping unwanted traffic before it reaches your network.
Black hole routing can quickly neutralize volumetric attacks but must be is not ideal as the network will still be inaccessible to legitimate traffic.
3. Load balancing and traffic management
Distributing incoming traffic across multiple servers prevents any single server from becoming overwhelmed.
Load balancers ensure availability even during high traffic volumes.
4. Content delivery networks (CDNs)
CDNs reduce attack impact by distributing traffic across a global server network, helping to maintain site performance during DDoS events.
5. AI-driven detection and automated response
AI-based tools detect and mitigate threats by analyzing traffic patterns in real time. Autonomous response tools buy back time for security teams to effectively execute a response strategy.
Automated response systems minimize downtime by neutralizing attacks before they escalate.
Best plan of action
- Adopt a multi-layered security strategy, combining WAFs, black hole routing, CDNs, and AI-based tools.
- Regularly monitor network traffic, conduct stress tests, and update security protocols.
- Develop a rapid-response plan to ensure swift action when attacks occur.
Implementing these defenses helps mitigate threats, safeguard operations, and maintain service continuity.
How to Choose a Mitigation Provider?
When choosing a mitigation provider, take into consideration network capacity, processing capacity, scalability, flexibility, and reliability.
Network capacity
Your DDoS mitigation service needs to have enough bandwidth in its network to block the large volume of false traffic generated during an attack. For instance, if the network can handle 1 Tbps, it can block that much DDoS traffic—after taking into account the bandwidth used up by normal operations.
Processing capacity
A DDoS mitigation strategy needs to be able to process a large amount of data quickly. One of the DDoS mitigation steps is processing and forwarding traffic. For example, if an attack is coming in at a rate of 75 million packets per second (Mpps) and your DDoS mitigation plan can only process 65 Mpps, some will get through to your server.
Scalability
Your DDoS mitigation service needs to be scalable because attack sizes are likely to grow rather than diminish. If your DDoS mitigation provider cannot increase its network or processing capacity, larger attacks in the future may be able to penetrate your server.
Flexibility
When defending against DDoS attacks, flexibility is as, if not more, important than rebutting ransomware or viral threats. The system needs to be adaptable to recognize attacks even when there are large fluctuations in legitimate traffic. This requires setting up page rules that differentiate real traffic from false, as well as control how an attack is mitigated. These rules have to be disseminated across the entire network.
Reliability
Your DDoS service, like a firewall, needs to be reliable. It should be there when you need it—every time. To ensure a reliable defense system, your service needs to have 24/7 oversight, as well as redundancy and failover solutions, which spin up “insurance” systems in the event a primary component fails.
How AI and Machine Learning can Protect you from DDoS Attacks?
AI-based cybersecurity solutions, such as Darktrace, empower security teams by improving Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR) when facing a DDoS attack. By continuously analyzing traffic patterns, AI tools detect deviations from normal behavior, enabling them to identify and mitigate attacks in real time, often before they escalate into full-scale threats.
Value of AI for real-time threat detection and defense
- Faster detection and response: AI-driven systems can process vast amounts of network data far more quickly than human analysts. This enables immediate identification of unusual traffic spikes or malicious patterns, leading to faster containment.
- Adaptive learning: Machine learning algorithms continuously evolve by learning from both successful and failed attempts to breach systems. This adaptability ensures that defenses remain effective even against emerging threats and evolving attack tactics.
- Autonomous protection: AI systems can autonomously take protective actions, such as throttling traffic, blocking suspicious IP addresses, or engaging black hole routing. This allows for continuous defense, even during off-hours when human intervention is limited.
- Operational efficiency: Automated threat detection reduces the burden on security teams, allowing them to focus on high-priority tasks rather than manually managing incident responses.
Business benefits
- Minimized downtime: Proactive DDoS defense ensures that critical services remain available, reducing revenue loss and reputational damage.
- Enhanced customer trust: Maintaining uninterrupted service during attacks helps businesses build trust with customers by demonstrating robust security measures.
- Scalable protection: AI tools can efficiently handle threats regardless of the size or complexity of the attack, making them suitable for businesses of all scales.
By leveraging AI, organizations gain a dynamic and scalable approach to combating DDoS threats, ensuring stronger security and resilience.
Real World Examples of DDoS Attacks?
Aisuru Botnet Attack (2025): Currently one of the largest recorded attacks, peaking at 29.7 Tbps. It was mitigated by Cloudflare and targeted various telecommunications and hosting providers.
Google (2023): Google mitigated a record-breaking HTTP/2 "Rapid Reset" attack that reached 398 million requests per second (RPS). This attack used a novel technique to rapidly open and cancel requests to exhaust server resources.
Microsoft Azure (2021/2023): Azure has faced several massive volumetric attacks, including a 3.47 Tbps assault in 2021 that originated from approximately 10,000 sources across 10 countries.
Amazon Web Services (2020): AWS reported a 2.3 Tbps attack that lasted for three days. It used CLDAP reflection, a technique that amplifies the volume of data sent to a victim by up to 70 times.
GitHub (2018): This attack was famous for achieving 1.35 Tbps without using a traditional botnet. Instead, attackers exploited misconfigured Memcached servers to amplify their traffic by 50,000 times.
Dyn DNS Attack (2016): One of the most disruptive events in history, the Mirai botnet (comprising hijacked IoT devices like cameras and routers) targeted the DNS provider Dyn. This effectively knocked major services like Netflix, Twitter, and Reddit offline for hours.
Estonia Cyberattacks (2007): Following a political dispute with Russia, Estonia's government, media, and banking sites were crippled for weeks. This is widely considered one of the first major acts of cyber warfare.
Gaming Industry (Ongoing): Platforms like PlayStation Network and Xbox Live were famously targeted by the "Lizard Squad" during Christmas 2014, affecting 160 million gamers. More recently, the LCK (League of Legends Korea) 2024 season faced persistent disruptions from DDoS.
Financial Sector: In 2012, the "Izz ad-Din al-Qassam Cyber Fighters" launched Operation Ababil, targeting major U.S. banks like Bank of America and JPMorgan Chase in multiple waves.
Summary
In the landscape of cyber security, DDoS attacks represent a persistent and growing threat, orchestrated by various actors with malicious intent. These attacks aim to disrupt online services by overwhelming them with malicious internet traffic, potentially causing harm to organizations. DDoS attacks come in different forms, including volumetric attacks that saturate network bandwidth, protocol attacks that exploit vulnerabilities in data transfer protocols, and application layer attacks that target application weaknesses.