Zero Trust Architecture (ZTA)
Zero trust Architecture is a modern and boundless security framework that follows the principle of “never trust, always verify”. This framework strictly mandates strict authentication for every user and device. ZTA minimizes the cyber-attack with least access to protect data and applications. ZTA allows only authorized person to access regardless of network location.

Core Idea & Fundamentals:
Never Trust, Always Verify: ZTA is based on this core principle which believes that no user is trusted by default. Any user can be a threat whether inside or outside the network location.
Least Security Access: Users have limited system access to complete their necessary chores only. Other than that they are not permitted to approach sensitive data.
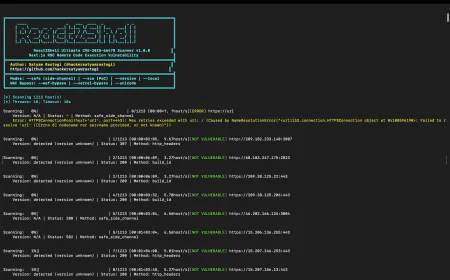
Continuous Scanning: Constantly verifying user’s identity and checking for system compliance ensures data security. Unauthorized users cannot get the permission for device access without complete verification.
Network Segmentation: Rather using a vast and disseminated channels ZTA framework divides network into small and secure segments to reduce data breaches.
Presume Suspect: Always assuming that any user can be potential threat whether it is inside the network or outside the location.
Device Security: Validating that systems are fully authorized and compliant before granting access.
Policy Access Only: Allows system access with company policy only. Responsible for secure communication gateway and access denied for threatful connections.
Advantage of Zero Trust Security:
Reduced Cyber Attack Platform: By authenticating every user access request ZTA minimizes the risk of data breaches.
Apparent Monitoring: Continuous user verification and system monitoring allows faster threat detection.
Improved Security: By constant system validation ZTA improves data security. Unauthorized user cannot get the access permission thus reduces the risk of data breaches.
Limited Access to Necessary Tasks Only: This security framework grants for least application access, only if they need to use for necessary job chores. Any inappropriate access would be denied for ensuring data security.
ZTA helps organizations to adhere strict compliance requirements by providing complete audit details and strict data access policy.
Prevents Repercussions: Once the initial setup is done ZTA reduces future financial losses caused by data breaches. It keeps devices fully verified and well compliant to avoid legal violations.
Secure Remote Network: ZTA provides advanced security even for remote networks. It allows users to work securely from any location without any risk.
Data-Centric Security: ZTA focuses on securing data itself rather its location. Sensitive data is always password protected and accessible only on need-to-know basis. When user requests to access any personal information Zero Trust Security always ask for a complete verification. Only after validating the user’s identity data would be accessible. This security measure prevents risks of sensitive data breaches.
Top Listed Zero Trust Architecture Tools:
Cloaudflare Zero Trust: Offers complete security including ZTNA, CASB, and Secure web gateway (SWG).
Zscaler: Securing user to application connections with ZTNA and SASE type services.
Palo Alto Networks: Provides a strong SASE service and platform based device access.
Okta Identity Cloud: Focuses on user identity verification. Ensures secure and authenticated access.
Microsoft Azure AD: Provides identity management security and access control also supports well with Microsoft programs.
Twingate: A simple ZTNA solution to replace traditional VPNs with secure access.
CrowdStrike: Focuses on (EDR) devise security by ensuring that devises are fully authenticated and compliant before using them.
Illumio: Specializes in network micro segmentation for better security and to prevent data breaches.
Beyond Trust: Leading in intelligent identity threat detection and access security.
StrongDM: Audits and manages infrastructure access with Zero Trust policy.
Categories of Zero Trust Tools:
Zero Trust Network Access (ZTNA): Allows application level access only instead of broad network usage for a secure operation.
Identity and Access Management (IAM): Secure access with strict user authentication for every request.
Microsegmentation: Dividing broad networks into small segments for controlled data access and to avoid cyber-attacks.
Secure Access Service Edge (SASE): Provides security services directly to the network regardless its origin.
Endpoint Detection and Response (EDR): Focusing on device security through authentication and ensuring that they are completely safe to use.
Cloud Access Security Broker (CASB): This solution offers strictly controlled access to cloud services and monitoring unauthorized access to protect system from potential threat.
Privileged Access Management (PAM): Verifies user’s identity and grants access permission to authorized user only.
Policy Decision Point (PDP): PDP is the brain of the architecture which evaluates user's access request whether that applies company policies and then allow or deny access to the requester.
Policy Enforcement Point (PEP): The PEP verifies access request and send valid details to the PDP then decides whether to approve or deny request.
Data Loss Prevention (DLP) & Encryption: Data loss prevention is a security solution that prevents extraction of sensitive data.
Security Information and Event Management (SIEM)/SOAR: SIEM solutions continuously collects data from various sources and identifies patterns to detect potential threats.
Conclusion:
The Zero Trust Architecture helps existing security controls perform better. This policy works on user verification, authentication, and validation. Without verifying the request this security framework strictly denies the access request and does not allow to reach out to any personal information. This model helps organizations to improve their security controls and reduce data breaches. Also, it provides modern security with trust that significantly cuts-down the unauthorized access happenings.