Salesloft OAuth Breach via Drift AI Chat Agent Exposes Salesforce Customer Data
A sophisticated cyberattack leveraging compromised OAuth tokens from the Salesloft Drift AI chat agent has allowed threat actors—tracked as UNC6395—to access numerous Salesforce customer environments. Between August 8 and 18, 2025, they exfiltrated highly sensitive credentials including AWS access keys, passwords, and Snowflake tokens before being cut off by Salesloft and Salesforce.
Incident Overview
In mid-August 2025, a threat actor identified by Google Threat Intelligence Group (GTIG) and Mandiant as UNC6395 exploited stolen OAuth and refresh tokens associated with the Salesloft Drift AI chat agent integration with Salesforce. From August 8 to 18, they infiltrated dozens of Salesforce environments to extract critical credentials like AWS access keys (AKIA), passwords, and Snowflake access tokens.
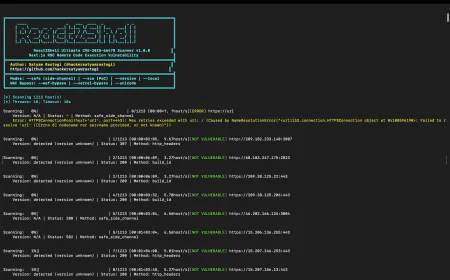
Attack Execution & Tactics
Using the compromised tokens, the attackers executed SOQL queries against Salesforce objects—such as Cases, Accounts, Users, and Opportunities—to harvest sensitive secrets. Demonstrating operational stealth, they deleted query jobs to conceal activity, though audit logs remained intact
Response by Salesloft and Salesforce
On August 20, 2025, Salesloft and Salesforce collaborated to revoke all active OAuth and refresh tokens tied to the Drift application. Salesforce also removed Drift from its AppExchange pending further investigation, and impacted customers were notified.
Scale & Attribution
Google’s GTIG estimates that over 700 organizations may have been targeted in this campaign. The primary objective appears to be credential harvesting for future exploitation or lateral movement activities.
Why This Breach Matters
This incident highlights a growing risk vector: SaaS-to-SaaS supply chain attacks. Legitimate OAuth-enabled integrations can become attack vectors if insufficiently governed. Persistent tokens, broad access scopes, limited monitoring, and insecure storage of secrets all contributed to the success of this breach.
Recommended Mitigation Steps
-
Reauthenticate Integrations: Disconnect and reconnect the Salesloft Drift integration under Settings > Integrations > Salesforce to invalidate compromised tokens
- Rotate Secrets: Immediately revoke and rotate any AWS keys, Snowflake tokens, passwords, and other credentials found in Salesforce objects.
- Review Logs: Check audit logs—including User-Agent strings such as
python-requests/2.32.4,Salesforce-Multi-Org-Fetcher/1.0, and others—for suspicious activity. Look for evidence of query jobs, Tor exit node connections, and other anomalies
- Implement Principle of Least Privilege: Restrict connected app scopes and enforce IP-based restrictions using Salesforce’s ‘IP Relaxation’ policy.
- Enhance Monitoring: Use UEBA and aggregated log analysis to detect abnormal behavior in third-party integrations
Conclusion
The breach of Salesloft's Drift integration demonstrates how third-party OAuth relationships can become critical security gaps if not properly managed. The careful planning and stealth exhibited by UNC6395 underscore the need for vigilance across SaaS ecosystems. Organizations must treat OAuth-enabled tools as potential risk vectors and enforce rigorous control, monitoring, and incident response.
Immediate Actions:
-
Disconnect and reauthenticate Drift integration.
-
Rotate all exposed credentials.
-
Audit logs and apply controls to connected apps.
-
Review your security posture around third-party integrations.